 Apple’s ongoing battle with the FBI has big implications for our HIPAA compliance when we use iPhones in practice.
Apple’s ongoing battle with the FBI has big implications for our HIPAA compliance when we use iPhones in practice.
For some background: nerds (like us) everywhere have been buzzing about Apple’s taking a stand against an FBI subpoena. Apple is refusing to help them unlock the iPhone that belonged to San Bernardino shooter Sayed Farook.
The FBI’s data forensics experts are stymied by the fact that all relatively recent iPhones automatically employ full-device encryption. They cannot get past the encryption without using the old-fashioned method of simply guessing its PIN code.
The fact that the FBI finds themselves in this position is not a good sign for anti-terrorism investigation, but it’s a good sign for health professionals who need to secure protected health information.
Here are 3 things we learn from it:
1) This is a big, dramatic test of the iPhone’s ability to protect the confidentiality of its contents, and it seems to be earning an “A”
Ever since version 8.0 of the iPhone software, Apple has claimed that their popular smartphone uses a thing called “full-device encryption.” Those who are regular readers here will know the significance of that jargony term. HIPAA’s Breach Notification Final Rule has a safe harbor in it for information storage gizmos that use full-device encryption (read our article about the Breach Notification Final Rule here.)
To cursorily explain what that means: HIPAA assumes that a device with properly enacted full-device encryption is essentially impenetrable. If such a device is lost or stolen, HIPAA Covered Entities can lean on the full-device encryption to keep the lost information safe from prying eyes.

“I have to tell you: an anonymous person has all the text messages and emails you ever sent me”
“What?? Did he mug you for your phone? Did he steal your phone from your bag???”
“Uh… I left it in the bathroom at Starbucks”
That means that if you lose your iPhone, full-device encryption can mean the difference between simply mourning the loss of an expensive gadget and having to tell all your clients and also the federal Office of Civil Rights that you lost their confidential information (we have more on encryption and HIPAA here.)
The iPhone is a complicated beast, however, and hackers have been poking holes in its security since day one. The bold effectiveness of its encryption scheme is theoretically great, but it’s better to see things like this tested in the wild before we lean on them. The fact that even the FBI find themselves stymied by the phone’s encryption is a strong endorsement of its effectiveness for keeping client information confidential.
The whole story on full-device encryption and HIPAA is not what this article is about. But you can read about it — and get CE credit for your time — in our free 1-hour CE guided reading course that is available at no cost to our (also free) newsletter subscribers. Click here to learn more about that. →
“But Roy,” you say, “I heard that the FBI actually can unlock the iPhone whenever they want and this case is just for PR.”

Can the FBI crack this iPhone by doing science to it?
(joke hint: “H2O, too” → H2O2)
There’s been a lot of discussion about whether or not the FBI actually needs Apple to get involved in order to unlock this phone. Theories range from just assuming that Farook probably didn’t have his “Data Protection” setting turned on (more about that below) to using a risky-yet-ingenious combination of lasers, acid, and Faraday cages to bypass the need for Apple’s help altogether. (citation: Ars Technica)
Here’s the rub, though: none of those wacky techniques has anything to do with actually breaking the phone’s encryption.
iPhone Feature: “Data Protection”
What the FBI wants Apple to do is create a new operating system for this particular phone that allows the FBI to make unlimited guesses as to what its PIN code is. For iPhones with the Data Protection feature turned on, guessers are limited to just 10 guesses before the phone automatically “bricks” itself as a protective measure and the information on it becomes irretrievable forever and ever.
All the theories presented about how the FBI could break into the phone without help from Apple are entirely about getting past the Data Protection piece. The only consequence of bypassing Data Protection would be that the FBI gets infinite chances at guessing the PIN code. Which brings us to:
Our free, informative articles are brought to you by Hushmail,
who is offering our readers 15% off for life!
Wondering why this is here? See our sponsorship policy for details.

 Roy says: Hushmail is one of several secure email options that serves health care practitioners like us. Hushmail is highly trusted, affordable, includes secure web forms that accept e-signatures, and has earned a recommendation from us for use by mental health professionals. Learn more about Hushmail for Healthcare and get 15% off for life.
Roy says: Hushmail is one of several secure email options that serves health care practitioners like us. Hushmail is highly trusted, affordable, includes secure web forms that accept e-signatures, and has earned a recommendation from us for use by mental health professionals. Learn more about Hushmail for Healthcare and get 15% off for life.
2) We really need good PIN codes on our iPhones!
The only reason the FBI is pursuing this case with Apple is that they believe the phone to be protected by just a simple, 4-digit PIN code. That 4-digit code is the only thing holding the device’s encryption in a locked state.
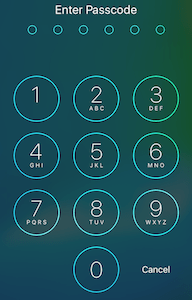
The default iPhone PIN code screen
So let’s look at the math: a PIN code with 4 digits has 4 possible spots for a character, with each spot containing 10 possible characters (the digits 0-9 make a total of 10 possible characters.) If I’m remembering my high school algebra correctly, that means that a 4-digit PIN has up to 10,000 possible combinations.
10,000 possible PIN codes may seem like a lot, but it ain’t.
If the FBI gets what they want, and they are able to hook up the phone to one of their own computers and make infinite guesses without penalty, they’ll be able to make guesses as fast as the phone can physically accept guesses.
Apple says the iPhone can manage one PIN code guess every 80 milliseconds. So guessing all 10,000 possible PIN codes would take 800 seconds, or less than 15 minutes. So a 4-digit PIN code could keep the FBI out of the phone for an average of 7 minutes.
That’s why the FBI wants Apple to bypass the Data Protection feature and the extra time delay between PIN code guesses. With that barrier eliminated, they figure they can get into the phone lickety-split.
Imagine if we use a 6-digit PIN instead of a 4-digit one. The newer iPhones default to 6 digits instead of 4, so many of you reading this may have such a PIN code on your phone already. 6 digits makes for 1,000,000 combinations! That ought to do it, right? Well, not really. Guessing all the PINs would take just under 24 hours, for an average wait of 12 hours before the phone is opened.

iPhone password screen when alphanumeric passwords are turned on
What if we go into the Settings app on our iPhones and make a radical change? We switch from using just numeric digits to using the full array of alphanumeric characters one can find on a keyboard. After doing that, the number of possibilities per spot in the password (now it’s a “password,” not just a “PIN code”) rises far above just the 10 numeric digits we had when we used a basic PIN code.
Let’s skip the math and get to the bottom line on that one: I estimate that for a 6-character password with numbers, upper and lower-case letters, and punctuation, it would take a little over 350 years to guess all the possibilities.
So on average it would take the FBI over 175 years to get into an iPhone with a well-created 6 character password — even with Apple’s help.
Some vital password tips:
If your password is mostly just a word that could be a found in a dictionary, or even variations on that word with additional numbers or punctuation characters, it will be guessed far, far faster. If you wish to use recognizable words in your password, you’ll need to use a well-created passphrase.
At Person-Centered Tech, our official recommendation is that you use at least an 8-character, alphanumeric password on your iPhone. Roy uses a 20 character password.
If you have an iPhone 5s or newer iPhone, you can make it easy to do this by activating the fingerprint feature. That lets you unlock your phone without entering your password every time you need to get into it (because you just press your thumb to the button and it opens right up.)
3) The safe harbor in HIPAA’s Breach Notification Final Rule requires more than just turning encryption on
 The breach notification rule’s safe harbor for full-device encryption will apply if the device is reliably encrypted at the time when the encryption comes up as needed. That means:
The breach notification rule’s safe harbor for full-device encryption will apply if the device is reliably encrypted at the time when the encryption comes up as needed. That means:
- Encryption with a weak password is the same as no encryption at all, so far as HIPAA is concerned.
- On iPhones, your encryption may not mean much if you don’t turn on Data Protection.
- An undiscussed-but-still-vital point: to make sure your iPhone is not prone to hackery, you absolutely must keep the software updated. You also absolutely must change your settings to disallow Siri in the lock screen.Yes, that means you’ll have to enter your passcode before you can use Siri. However, pretty much every hack in existence that can bypass the iPhone’s password relies on old phone software or on vulnerabilities in Siri.
So simply turning encryption on is not the whole story for protecting our devices in a HIPAA-secure fashion. If we do support the encryption properly, though, it does wonders for our security, our clients’ safety, and our HIPAA compliance.
Beyond iPhone Encryption
This whole article talks about just one risk posed to information that we keep on iPhones: the risk of confidentiality breach if the iPhone gets lost and a bad guy sees what information we have stored on that phone.
There are numerous other security risks faced by information on smartphones and a bunch of different things we can do to mitigate those risks. We will likely discuss more about them on this website, but they are covered thoroughly by materials in our Digital Confidentiality course series.

A very informative article …I have taken care of my SIRI access and will f/u on the password info you gave ASAP. How does one “turn on Data Protection” on an iPhone ??
Thank you Roy !
Hi Shelly,
Try a Google search for “How to turn on iPhone data protection.” :)
You can also search for tuts on creating a stronger password, or our Person-Centered Tech Support subscribers have a video demonstrating it here: https://personcenteredtech.com/vidhelps/how-do-i-set-a-strong-password-on-my-smartphone-or-tablet/#ios
Well, I guess I have to buy an iPhone now… ? Thanks once again for the great info, Roy!
Ha. :) Don’t forget that Android phones can do full-device encryption, too!
Yeah, but really, I just needed an excuse. ;-)
Oh, well I’m happy to provide, then! :)
The recent breach of WhatsApp (by the NSO Pegasus program) that allowed unanswered WhatsApp voice calls to overcome 256bit encryption on phones, and then to take full control of said phone(beyond WhatsApp sandbox) has me spooked. How can ever have a HIPAA safe harbor smartphone again? Ideas?
Hello! We aren’t Dixie Cup aficianados either. There are some less spooky options out there. Check out our HIPAAppropriateness Texting App reviews here! Hope these help.